VNS3:ms Overview
VNS3:ms Setup
Monitoring Cloud
Monitoring VNS3
VNS3:ms MFA
VNS3 Firewalls
High Availability (HA)
Triggering HA Events
VNS3 Controller Passwords
Managing Snapshots
User Administration
General Settings
VNS3:ms Backup
Installing SSL
Auditing
Remote support
Release Notes
VNS3:ms EOL Policy and Milestones
Monitoring Cloud
Create a Cloud Virtual Network
Virtual Networks is the primary taxon or classification unit in the VNS3:ms taxonomy. Virtual Networks are comprised of VNS3 Topologies and Cloud VLANs.
To create a Virtual Network, click on New Virtual Network from the left column menu.
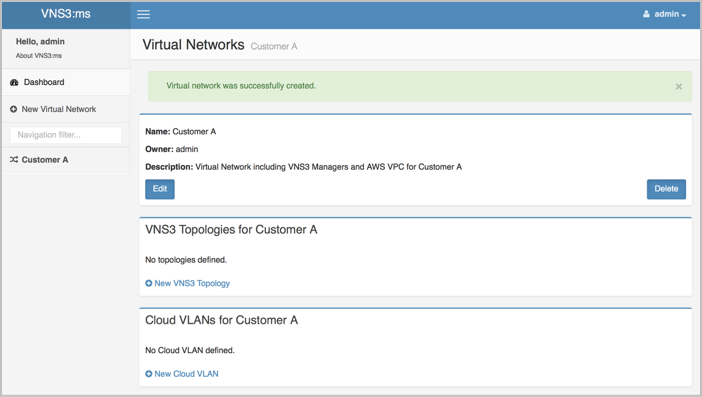
On the resulting page give a name and description for your Virtual Network and click Save.

The Virtual Network object will be created and listed in the left column menu.
Add Cloud Credentials: IAM policy or Access Keys
In order to add a Cloud VLAN to to the VNS3:ms monitor and management system, cloud credentials must be added to the VNS3:ms instance in order to collect the relevant VLAN information from the cloud provider.
Recommended best practices are to use an AWS IAM Role attached to the VNS3:ms instance for temporary/dynamic AWS API keys (NOTE: IAM roles do support cross account access).
In situations where the IAM Role aren’t an option, long term/static API credentials can be used but it is recommended that a specific IAM programatic access account is created for the VNS3:ms system. This can be done by attaching the Policy found below to a new IAMs User. The IAM User’s Secret Access Key and Access Key ID are required to create the Cloud Credential in VNS3:ms.
The Role or User associated with the Cloud Credential requires the following Policy to provide the necessary permissions to the VNS3:ms instance:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "ActionsRequiredforVNS3msVLAN",
"Effect": "Allow",
"Action": [
"ec2:DescribeAddresses",
"ec2:DescribeAvailabilityZones",
"ec2:DescribeClassicLinkInstances",
"ec2:DescribeCustomerGateways",
"ec2:DescribeDhcpOptions",
"ec2:DescribeEgressOnlyInternetGateways",
"ec2:DescribeFlowLogs",
"ec2:DescribeImageAttribute",
"ec2:DescribeImages",
"ec2:DescribeInstance*",
"ec2:DescribeInternetGateways",
"ec2:DescribeNatGateways",
"ec2:DescribeNetwork*",
"ec2:DescribePrefixLists",
"ec2:DescribeRegions",
"ec2:DescribeRouteTables",
"ec2:DescribeSecurityGroupReferences",
"ec2:DescribeSecurityGroups",
"ec2:DescribeStaleSecurityGroups",
"ec2:DescribeSubnets",
"ec2:DescribeTags",
"ec2:DescribeTransit*",
"ec2:DescribeVpc*",
"ec2:DescribeVpn*"
],
"Resource": "*"
}
]
}
Start with EC2 read-only access. NOTE: If you plan on using VNS3:ha, you will need to provide some edit/full access capabilities to the VNS3:ms instance. See the VNS3:ha section for information.

To add cloud credentials click on the admin top right corner drop down menu, then click on Cloud Credentials.
Click Add Cloud Creds then enter the following information:
- Name
- Description
- Credentials type - cloud provider that the credentials are associated. Initially AWS is supported with more clouds coming soon.
- Use VNS3:ms IAM Role - check this box if using IAM Role for API access as recommended above.
- Account ID
- Access Key
- Secret Key
- GovCloud - is this a Gov Cloud account or generic AWS
Click Save.

Create Cloud VLAN
Return to the Virtual Network Page and click New Cloud VLAN.

Enter a Name and Description of the Cloud VLAN and click Save.

Specify a Cloud VLAN Component to Monitor
From the resulting Cloud VLAN page, click Add New VLAN Component.

Enter a Name and Description of the Cloud VLAN and click Save.
Enter the following information for the Cloud VLAN Component to be monitored:
- Name
- Description
- Cloud Credentials - specify the credentials that were just added
- VLAN Component Region - region where the VLAN component is setup
- VPCs - select from a list of VPCs in the region specified
Click Save.

Cloud VLAN Component Status Page
Information on the Cloud VLAN Component Status page is broken down into component identification information surfaced by the cloud provider (e.g. vpc-id, subnet ids, etc. ).
VNS3:ms then stitches together all the information into a single easy to consume page. The relevant information VNS3:ms provides is:
- Addresses - the instances currently running in the VLAN
- Routes - the routes setup in the VLAN that are being used by the VLAN instances
- Rules - ACL and Security Group rules for the VLAN and the instance running in the VLAN

Updated on 27 Apr 2020
